Advanced Internet Platform 516527835 Guide

The Advanced Internet Platform 516527835 Guide presents a disciplined blueprint for secure, scalable systems grounded in measurable, repeatable processes. It emphasizes baseline controls, traceability, and least-privilege access, then ties decisions to data rather than conjecture. The document treats real-world load, latency, and cache strategies as core inputs, not afterthoughts. Growth is planned with modular, stateless designs and automated capacity planning. Its methods invite scrutiny and could change how teams justify next steps. This framework warrants close consideration.
Set Up Secure 516527835: Core Steps and Best Practices
Setting up Secure 516527835 involves establishing a formal baseline of security controls, configurations, and monitoring that collectively reduce risk to an acceptable level.
The approach prioritizes repeatable procedures, traceable changes, and objective verification.
Security auditing provides evidence-backed insight, while access control enforces least-privilege access.
Decisions rest on data, not assumptions, balancing autonomy with responsible oversight for robust, adaptable protection.
Tune Performance for Real-World Loads
Real-world workloads expose gaps between baseline security configurations and runtime performance needs, requiring a measured adjustment of controls, routing, and resource allocation without compromising established protections. In practice, latency profiling informs threshold tuning, while cache warming aligns cold-start behavior with steady-state patterns.
The analysis favors data-driven decisions, evaluating tradeoffs, and preserving freedom to adapt configurations as load variances emerge.
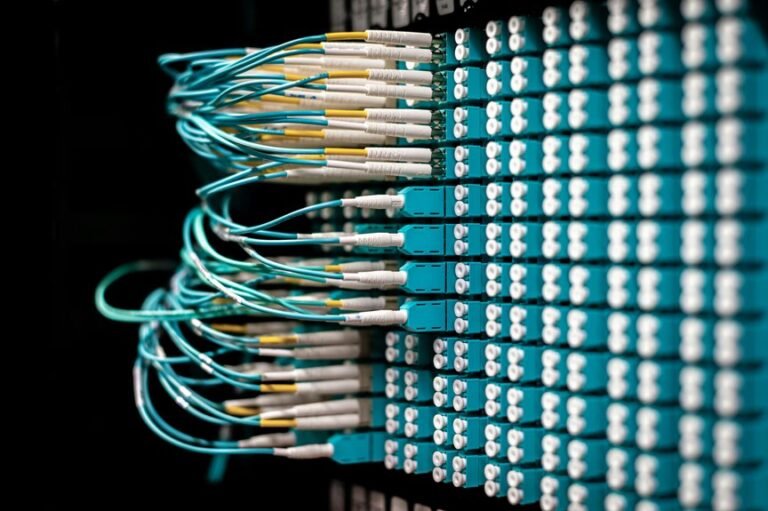
Scalable Architecture: Planning for Growth and Reliability
How can a scalable architecture accommodate growth while preserving reliability? A data-driven assessment outlines a layering approach, balancing elasticity and control. The scaling strategy prioritizes modular services, stateless design, and automated capacity planning. Fault tolerance is embedded via redundancy, graceful degradation, and failure-isolation. Trade-offs are quantified, guiding investment in observability, testing, and progressive rollouts to sustain performance under expanding demand.
Practical Workflows: Troubleshooting and Next-Step Optimization
Practical workflows for troubleshooting and next-step optimization emphasize a disciplined, data-driven approach to diagnosing issues, validating hypotheses, and guiding iterative improvements. The narrative remains detached, emphasizing evidence over assertion. Concept mapping clarifies interdependencies, while risk assessment weights potential failures and mitigations. Decisions emerge from structured tests, repeatable analyses, and transparent criteria, enabling principled advancement without dogma or premature conclusions.
Conclusion
In the ledger of progress, the platform stands as a starken lighthouse: a beacon where data lines the rocks and navigation charts lie etched in code. Security, performance, and modularity are the harbor lights, constant yet adaptable. Change drives the tide, but traceable ships sail with least privilege as ballast. Growth arrives as a patient current, predictable and scalable. With disciplined workflows, ambiguity sinks, and the voyage toward reliable, dogma-free advancement remains charted and swift.